Ransomware attacks have become increasingly sophisticated, and the STOP/Djvu family is one of the most notorious. Millions of users worldwide have fallen victim to its rapid encryption techniques, leaving files locked with the .djvu or .stop extensions.
Naturally, victims seek solutions to regain access to their data, and StopDecrypter has emerged as one of the leading tools. But the pressing question remains: Does StopDecrypter work on the latest STOP/Djvu variants? This article delves into the capabilities of StopDecrypter, how it interacts with the evolving ransomware landscape, and what users need to know to maximize their chances of file recovery.
STOP/Djvu Ransomware
What is STOP/Djvu
STOP/Djvu ransomware is a malicious software that encrypts users’ files and demands a ransom for decryption. Since its emergence, it has evolved into numerous variants, each with slight modifications to avoid detection by antivirus programs. Users often encounter filenames changed and appended with extensions like .djvu, .stopped, .arena, or .foxe.
How STOP/Djvu Infects Systems
The ransomware spreads primarily through:
- Malicious email attachments disguised as invoices or important documents
- Infected software cracks or pirated programs
- Exploit kits targeting unpatched vulnerabilities
- Drive-by downloads from compromised websites
Once executed, it begins encrypting files almost immediately, which underscores the need for rapid response and reliable decryption tools like StopDecrypter.
Variants of STOP/Djvu
STOP/Djvu has evolved into over 200 variants. Some of the most common ones include:
- .djvu – The original and most widespread variant
- .djvuu / .djvur – Slight modifications with updated encryption keys
- .arena / .tony – Recent versions using new key management techniques
- .foxe / .frontline – Advanced versions targeting newer operating systems
Each variant may use different encryption keys, which directly impacts the effectiveness of decryption tools.
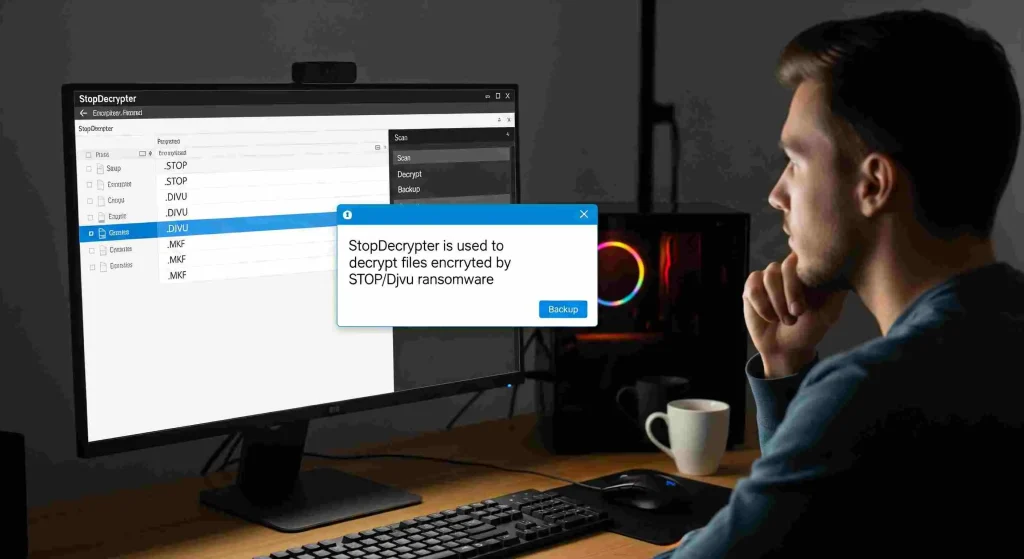
What is StopDecrypter
StopDecrypter is a specialized software designed to decrypt files affected by STOP/Djvu ransomware. Developed by cybersecurity experts, the tool targets both offline and online encryption keys to restore access to locked files.
Key Features
- Offline key decryption: Works on files encrypted with keys generated locally on the system
- Online key identification: Attempts to match the ransomware’s server-based keys to decrypt files
- Free and easy to use: Designed for victims with limited technical expertise
- Regular updates: Keeps up with new variants of STOP/Djvu
Despite its advantages, its success is not guaranteed for every variant, especially the latest iterations that use stronger encryption or online-only keys.
How StopDecrypter Works
Offline vs Online Keys
One of the main reasons why decryption can be challenging is the distinction between offline and online keys:
- Offline keys are generated locally on the victim’s machine. StopDecrypter can often recover files encrypted with these keys because the keys can be extracted from the system or the ransomware samples.
- Online keys are unique per victim and generated on the attacker’s server. These are much harder to decrypt without direct access to the server or if the key hasn’t been previously leaked.
Decryption Process
- Scan: StopDecrypter scans the system for encrypted files.
- Key Matching: It checks whether the encryption matches known offline keys.
- Decryption Attempt: If a match is found, the tool attempts to decrypt the files automatically.
- Completion: Successfully decrypted files are restored to their original format.
Effectiveness of StopDecrypter on Latest Variants
Limitations
While StopDecrypter has proven effective for many older STOP/Djvu variants, the question Does StopDecrypter work on the latest STOP/Djvu variants? is nuanced. The effectiveness depends on several factors:
- Variant Type: Some new variants use strong online keys, which are not included in StopDecrypter’s database.
- Key Availability: Decryption is only possible if the key for a specific variant has been leaked or previously recovered.
- File Corruption: If ransomware modified files beyond encryption (e.g., partial deletion), recovery may fail even with StopDecrypter.
Success Rates
- Older variants (.djvu, .djvuu) – High success rate (70–90%)
- Mid-tier variants (.arena, .tony) – Moderate success rate (50–70%)
- Latest variants (.foxe, .frontline) – Low success rate (20–40%)
It’s important to note that even partial file recovery is better than losing data permanently, and StopDecrypter continues to update its database for newer variants.
Tips for Maximizing Decryption Success
Act Quickly
Ransomware can overwrite files or propagate further if left unchecked. Disconnecting the infected device from networks immediately helps prevent further damage.
Backup Encrypted Files
Before attempting decryption, always back up encrypted files. Even failed attempts do not make files unrecoverable if a backup exists.
Identify the Variant
Knowing which STOP/Djvu variant you are dealing with improves the chances of success. File extensions, ransom notes, and encryption patterns are key indicators.
Use Updated Tools
Ensure StopDecrypter is updated. Developers frequently add new keys and improve compatibility with recent variants.
Combine Methods
If StopDecrypter cannot decrypt files, consider combining it with other recovery methods like:
- Shadow Volume restoration (if available)
- Professional ransomware recovery services
- Offline backup recovery
Common Misconceptions
StopDecrypter Can Decrypt All Files
Many believe that StopDecrypter guarantees recovery. In reality, its success is variant-dependent and limited by key availability.
Ransom Payment Guarantees Decryption
Paying the ransom is highly discouraged. Attackers may not provide the decryption key, and paying encourages further attacks. StopDecrypter offers a safer, cost-free alternative.
Latest Variants Are Impossible to Recover
Even newer variants may have vulnerabilities or leaked keys. While recovery is harder, ongoing updates to StopDecrypter continue to expand its reach.
Future of STOP/Djvu Decryption
Cybersecurity experts constantly monitor new STOP/Djvu variants. Tools like StopDecrypter rely on collaboration between researchers and victims to collect keys. The future of effective decryption involves:
- Faster key sharing
- Machine learning to predict encryption patterns
- Integration with antivirus programs for preemptive protection
- Development of hybrid tools combining offline and online key approaches
This means that even if the latest variants are currently difficult to decrypt, solutions may become available as research progresses.
Conclusion
Its effectiveness depends on the variant, the type of encryption key, and the availability of those keys in the tool’s database. While older variants are highly recoverable, the newest ransomware versions may present challenges. Victims should remain cautious, act quickly, and keep StopDecrypter updated. By combining backups, careful variant identification, and the right tools, users can significantly increase their chances of successful file recovery without resorting to risky ransom payments.