The question comes up repeatedly among cybersecurity professionals, IT administrators, and everyday users who suddenly find their files locked and inaccessible. Ransomware has evolved into a highly organized cybercrime ecosystem, and not every decryption tool works against every threat. StopDecrypter stands out because it was designed with a very specific ransomware lineage in mind.
Understanding that lineage is critical, not just for recovery, but for prevention, response planning, and realistic expectations when dealing with encrypted data. In this in-depth article, we will explore the ransomware family StopDecrypter focuses on, how that family operates, why the tool works the way it does, and what users should know before relying on it.
Ransomware Families
Before directly answering Which ransomware family does StopDecrypter target?, it is important to understand how ransomware families are defined. A ransomware family is a group of malicious programs that share core code, encryption methods, infrastructure, and operational patterns. Variants within the same family may look different on the surface, use different file extensions, or display different ransom notes, but internally they behave in similar ways.
This shared structure allows security researchers to analyze one sample and apply that knowledge to many related strains. StopDecrypter was built precisely because one ransomware family reused its design extensively, creating an opportunity for partial file recovery.
The Origin of StopDecrypter
StopDecrypter did not appear randomly or as a generic solution. It emerged in response to a massive surge of infections from a single ransomware group that flooded the internet with new variants every few weeks. Each variant changed file extensions and ransom messages, but the underlying encryption logic remained similar. Researchers noticed patterns in key generation and server communication that could sometimes be exploited. This observation leads directly back to the central question: Which ransomware family does StopDecrypter target? The answer lies in a family known for its scale, persistence, and adaptability.
The STOP/Djvu Ransomware Family Explained
The ransomware family targeted by StopDecrypter is widely known as STOP, also referred to as Djvu based on some of its early file extensions. This family has been active for years and is one of the most prolific ransomware operations ever observed.
STOP/Djvu primarily targets individual users and small businesses rather than large enterprises. It spreads through malicious software installers, cracked applications, fake updates, and deceptive downloads. When discussing Which ransomware family does StopDecrypter target?, STOP/Djvu is the definitive and precise answer.
Why STOP/Djvu Became So Widespread
STOP/Djvu’s success comes from its distribution strategy rather than technical sophistication alone. Attackers behind this family rely on volume. They compromise thousands of systems daily by bundling ransomware with pirated software or misleading installers.
This approach requires minimal targeting but yields massive infection numbers. Because STOP/Djvu variants share a common structure, StopDecrypter was developed to address that specific ecosystem. This is why the question Which ransomware family does StopDecrypter target? cannot be answered with a broad statement like “many ransomware types.” It is highly focused.
Encryption Behavior of STOP/Djvu
One reason StopDecrypter exists at all is due to how STOP/Djvu handles encryption keys. The ransomware uses a combination of offline and online encryption modes. When the infected system cannot reach the attacker’s server, it falls back to a locally stored offline key.
Security researchers have managed to collect many of these offline keys over time. StopDecrypter leverages that database. This technical detail is crucial when answering Which ransomware family does StopDecrypter target?, because not all ransomware families make this kind of mistake.
Online Keys vs Offline Keys
To fully understand Which ransomware family does StopDecrypter target?, we must explore the key distinction between online and offline keys. STOP/Djvu generates a unique online key when it can contact its command server. Files encrypted with this key cannot be decrypted without attacker cooperation. However, when the malware operates offline, it uses a shared offline key. StopDecrypter works only when files were encrypted using known offline keys. This limitation defines both the strength and the weakness of the tool.
Variants Within the STOP/Djvu Family
STOP/Djvu has produced hundreds of variants, each identified by a different file extension such as .djvu, .rumba, .npsk, or .promos. Despite these cosmetic changes, the core ransomware family remains the same. This consistency answers Which ransomware family does StopDecrypter target? with clarity: it targets STOP/Djvu variants that follow the same encryption framework. Users often assume that a new extension means a new family, but that is rarely the case with STOP/Djvu.
Why StopDecrypter Does Not Work on All Ransomware
Many users misunderstand the purpose of StopDecrypter, assuming it is a universal solution. It is not. The tool was never intended to decrypt files from unrelated ransomware families like Ryuk, LockBit, or REvil. Those families use entirely different cryptographic schemes. This reinforces the importance of knowing Which ransomware family does StopDecrypter target? Using the tool outside its intended scope leads to false expectations and wasted time.
The Role of Malware Researchers
StopDecrypter is the result of extensive reverse engineering by malware analysts who studied STOP/Djvu samples over a long period. Their work involved tracking command-and-control behavior, analyzing encryption routines, and collecting offline keys. The question reflects years of focused research rather than a generalized effort against ransomware as a whole. This specialization is what makes the tool effective within its limits.
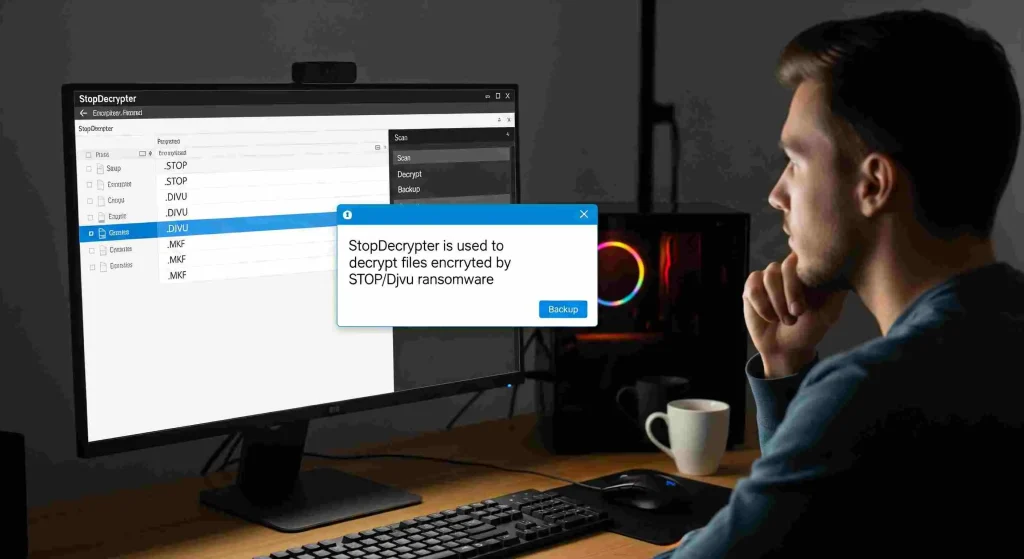
How StopDecrypter Identifies STOP/Djvu Infections
StopDecrypter does not guess randomly. It analyzes encrypted files, ransom notes, and metadata to determine whether the encryption matches known STOP/Djvu patterns. If it detects a compatible offline key, it attempts decryption. If not, it informs the user that recovery is not possible at this time. This technical precision further clarifies Which ransomware family does StopDecrypter target? and why its scope is intentionally narrow.
Common Misconceptions About StopDecrypter
A frequent misconception is that StopDecrypter failed if it cannot recover files. In reality, the tool may be functioning correctly but encountering files encrypted with an online key. Another misunderstanding is that StopDecrypter targets all ransomware that changes file extensions. In truth, when asked Which ransomware family does StopDecrypter target?, the answer remains singular and specific: STOP/Djvu and its compatible variants.
Evolution of the STOP/Djvu Family
STOP/Djvu continues to evolve, adapting its distribution methods and occasionally updating its encryption approach. However, the core design has remained stable enough for StopDecrypter to remain relevant. Each update to the ransomware family prompts renewed analysis to determine whether new offline keys can be extracted. This ongoing arms race is another reason for the question Which ransomware family does StopDecrypter target? remains relevant today.
Why Enterprises Rarely Use StopDecrypter
Large organizations are less frequently affected by STOP/Djvu because this family primarily targets individuals through pirated software. Enterprises usually face different ransomware families designed for high-value targets. Consequently, StopDecrypter is more commonly used by home users and small offices. This usage pattern aligns perfectly with the answer to Which ransomware family does StopDecrypter target?, reinforcing its consumer-focused design.
Risk Factors for STOP/Djvu Infection
Understanding Which ransomware family does StopDecrypter target? also helps identify risk factors. Users who download cracked software, disable antivirus protections, or install unknown programs are far more likely to encounter STOP/Djvu. Recognizing these behaviors can prevent infection altogether, which is always preferable to relying on decryption after the fact.
Ethical Considerations Around Decryption Tools
Decryption tools like StopDecrypter play an important role in undermining ransomware profitability. By enabling victims to recover files without paying, they reduce the incentive for attackers. This ethical dimension is directly tied to Which ransomware family does StopDecrypter target?, because STOP/Djvu thrives on small ransom payments collected at scale. Disrupting that model weakens the entire operation.
What to Do If StopDecrypter Cannot Decrypt Files
If StopDecrypter reports that files were encrypted with an online key, users should preserve the encrypted data and ransom notes. New offline keys may be discovered in the future. Understanding which ransomware family does StopDecrypter target? helps users make informed decisions rather than panicking or paying a ransom prematurely.
Comparing StopDecrypter to Other Decryption Tools
Many decryption tools exist, each targeting a specific ransomware family. Some focus on legacy threats, while others address niche variants. StopDecrypter stands out for its focus on one of the most widespread consumer ransomware families. When evaluating tools, asking Which ransomware family does StopDecrypter target? is a model question that should be applied to any decryption solution.
Long-Term Impact of STOP/Djvu on Cybersecurity
STOP/Djvu has influenced how cybersecurity professionals approach ransomware analysis. Its scale demonstrated the importance of rapid variant classification and shared intelligence. StopDecrypter is a direct outcome of those lessons. The ongoing relevance of which ransomware family does StopDecrypter target? highlights how one ransomware group reshaped defensive strategies.
Prevention Is Still the Best Defense
While StopDecrypter provides hope in some scenarios, prevention remains essential. Regular backups, cautious download habits, and updated security software dramatically reduce risk. Understanding Which ransomware family does StopDecrypter target? should not replace good security hygiene but complement it.
The Future of StopDecrypter
As long as STOP/Djvu continues operating, StopDecrypter will likely remain relevant. Updates may expand the offline key database or improve detection accuracy. However, its scope will remain limited to its intended family. The question: Which ransomware family does StopDecrypter target? will continue to have the same answer, even as variants come and go.
Conclusion
So, which ransomware family does StopDecrypter target? The answer is clear and precise: the STOP/Djvu ransomware family and its many closely related variants. StopDecrypter was never meant to be a universal solution but a specialized tool built on deep analysis of a single, highly prolific ransomware group. By understanding this focus, users can set realistic expectations, avoid misinformation, and make smarter decisions during a ransomware incident. Knowledge, combined with prevention and proper response, remains the strongest defense against threats like STOP/Djvu.